Uncategorized
Why Criminal Gangs Target Base Transceiver Stations
Base transceiver stations function as the primary nodes for wireless communication across the country. These sites house specialized hardware that maintains the flow of digital data and voice signals for millions of mobile users. Criminal groups view these locations as sources of high-value materials that command high prices in secondary markets. This perspective treats telecommunications infrastructure as a collection of commodities rather than a public utility.
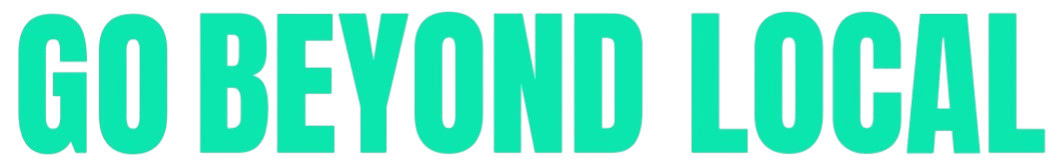
The demand for backup power solutions drives the theft of deep-cycle batteries from these installations. These batteries provide electricity when the primary power grid fails. A single site may contain multiple battery banks to ensure continuous operation. Each unit possesses a high resale price in the market for home solar systems and alternative energy setups. Consequently, the presence of these power storage units makes a station a prime location for organized theft. Criminal gangs often possess technical knowledge regarding the removal of these heavy components. They use specialized tools to bypass physical barriers and extract the batteries without damaging the internal lead or lithium cells. This activity results in immediate service outages for the surrounding community. In addition to batteries, the diesel fuel used to power onsite generators attracts criminal attention. Many stations in areas with unstable grid power rely on large fuel tanks to keep the equipment running. These tanks hold thousands of liters of diesel. The fuel serves as a liquid currency that is easily sold to transporters, small businesses, or residential users.
“The theft of diesel and batteries at our sites is a daily occurrence that affects the quality of service for subscribers.” — Gbolahan Awonuga, Head of Operations at the Association of Telecommunications Operators of Nigeria (ALTON), in a 2023 interview with The Guardian Nigeria.
Copper cables and grounding wires provide aher incentive for Base Transceiver Station Vandalism. Copper is a highly conductive metal with a global demand in the scrap metal industry. Thieves strip the thick cables that connect the antennas to the baseband units. They also remove the grounding systems that protect the equipment from lightning strikes. This removal of copper components causes long-term damage to the station. A site without a grounding system faces a high risk of equipment destruction during a storm. As a result, the cost of repair far exceeds the scrap value of the stolen metal. The service provider will spend millions to replace these connections while the thieves receive a small fraction of that value. Electronic modules and radio units also appear in the inventory of stolen items. These components contain specialized circuit boards and rare metals. While these parts are harder to sell than batteries or fuel, specific buyers in the international market seek them for refurbishing other systems. The loss of a single radio unit can disable a specific frequency band, which reduces the capacity of the network in that area.
“Vandalism of telecommunication infrastructure is a challenge to the quality of service in the country, with over 50, 000 cases of destruction and theft recorded in 2022 alone.” — Professor Umar Danbatta, former Executive Vice Chairman of the Nigerian Communications Commission (NCC), during a 2023 industry event.
The physical location of many stations contributes to their vulnerability. Many sites sit in isolated or rural areas where monitoring is difficult. Criminal gangs take advantage of the low human traffic to operate for extended periods. They may use heavy machinery to pull down perimeter fences or cut through reinforced steel doors. This means that the security of a station requires a multi-layered strategy. Physical barriers like concrete walls and steel cages provide a first line of defense. However, professional gangs often find ways to overcome these obstacles. Consequently, many operators now install remote monitoring systems that alert a central office when a door opens or a cable is cut. These technical solutions provide data on the timing and nature of the intrusion. If a sensor detects unauthorized activity, the system will trigger an alarm. This allows a security team to respond to the site. The presence of these systems acts as a deterrent for low-level thieves, though organized gangs may still attempt the theft.
The impact on the digital economy is a factual reality. When a station goes offline due to Base Transceiver Station Vandalism, local businesses lose access to point-of-sale terminals. Citizens are unable to perform mobile banking transfers or access emergency services. This disruption creates a ripple effect throughout the local economy, as modern commerce depends on constant connectivity. For a business owner in a rural area, a single night of vandalism at a nearby station will halt operations for days. The repair process involves sourcing replacement parts and transporting them to the site. If the damage is extensive, the restoration of service will take a long time. This delay affects the income of the business and the convenience of the residents. Statistics from the industry indicate the scale of the financial burden. The Nigerian Communications Commission (NCC) reported that the industry recorded over 1, 000 cases of fiber cuts and site vandalism in a single year. These incidents lead to a loss of billions of Naira in equipment and lost revenue. These figures highlight the requirement for enhanced protection of these assets.
“Between August 2022 and August 2023, the industry recorded over 1, 000 cases of fiber cuts and vandalism of base stations.” — Dr. Aminu Maida, Executive Vice Chairman of the Nigerian Communications Commission, during a stakeholder meeting in November 2023.
Community engagement serves as a practical method to reduce these incidents. Residents who live near a station may act as informal observers. When the community understands that their own connectivity depends on the safety of the equipment, they are more likely to report suspicious activity. This partnership between the operator and the local population improves the security of the infrastructure. Operators may also hire local security personnel to provide a physical presence at high-risk sites. This provides employment for the community and ensures a faster response to threats. A guard on site will prevent the use of heavy tools that thieves require to extract batteries or fuel. This human element a powerful addition to electronic sensors. In conclusion, criminal gangs target these sites because the components have immediate value in the shadow market. The theft of batteries, fuel, and copper creates a financial gain for the thieves while causing a large loss for the public. Protecting these sites involves a combination of hardened physical barriers, remote monitoring technology, and community cooperation. Maintaining the integrity of the telecommunications network will ensure that the digital economy continues to function for the benefit of citizens.
Digital Hustle
How One Misplaced Dot Broke a Bank Login Page
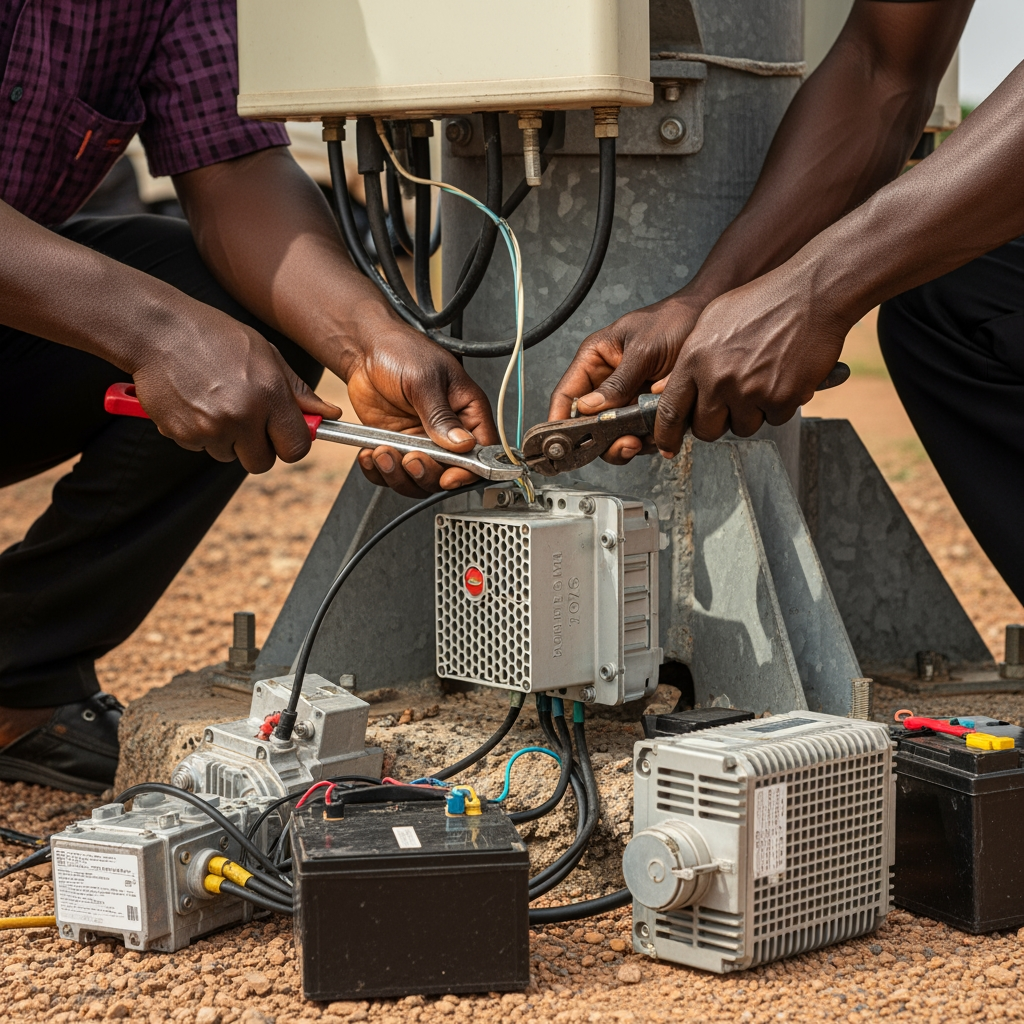
A bank login page is more than just a simple screen on a website. It is the secure doorway that allows customers to reach their online accounts. Every time someone enters their username and password, the page serves as the bridge that connects the user with their money. When this page works perfectly, people enjoy smooth access. When it fails, confusion rises, and trust is shaken. What many do not know is that even a small detail, as tiny as a dot in computer code, can decide whether this door remains open or completely shut. There was a day when one misplaced dot broke a bank login page and locked out thousands of customers.
In daily life, a dot may look ordinary, simply ending a sentence. But in programming, a dot carries a higher weight. It links commands, guides actions, and connects pathways inside the code. Every dot has a position where it belongs. If that dot shifts, the whole meaning of the code changes. When the dot sits correctly, the instructions flow smoothly, and systems stay strong. But when it stands in the wrong place, the connection breaks, and the page collapses. This was exactly what happened in that bank login page error. A small misplaced dot blocked access and turned the page into a wall instead of a door.
When customers tried to log in, the page rejected every password, even when the details were correct. Error messages flashed, and people believed their accounts had been blocked. In truth, the accounts were safe, but the login script had lost its way. The misplaced dot confused the code, stopping it from speaking with the main server. What seemed like a massive cyber-attack was nothing more than a hidden syntax error. This error was small in size but great in effect. It proves once again that even a tiny seed can grow into a tree that affects many lives. In the same way, one symbol in the wrong place affected thousands of customers in one day.
The technical team of the bank was forced into action. They began a deep review of the code, reading line after line like scribes searching for a missing mark. At last, they found it. A single dot stood in the wrong place. It looked harmless, but it was the stone in the engine. Once the dot was moved back into its correct position, the entire bank login page came alive again. Customers could access their accounts, and the noise of fear began to fade. That correction, though small, restored confidence. It is a clear picture of how a little mistake can block the path, and a little correction can restore the light.
For developers and financial institutions, this case shines a light on three truths. First, it shows the necessity of code review. When more than one pair of eyes checks the script, hidden faults are easily discovered. The misplaced dot slipped through the first check, but a second review could have stopped the crisis before it began. Second, it reveals the value of a testing environment. This is a space where the system can be tested with fake accounts before it meets real customers. If the login page had gone through stronger testing, the dot would have been caught in silence. Third, it proves that every small detail matters in digital security. While banks build firewalls and strong encryption to fight hackers, they must also protect against simple human mistakes. A misplaced dot costs nothing to fix but can cost everything in customer trust.
For ordinary users, this story uncovers the hidden world behind every online banking login. People see only a clean page where they type details, but behind that page is a chain of codes stretching like an invisible ladder. If even one step on that ladder breaks, the climb becomes impossible. Customers should understand that many errors come from technical mistakes, not always from hackers. This knowledge reduces panic and allows patience while systems recover. But for the bank staff, the story is a strong call that the trust of the people rests on their attention to detail. When they watch carefully over every line of code, they protect not just data but also peace of mind.
The world of computing has seen many similar cases. Programmers call such mistakes bugs in software. Some are small, like this misplaced dot, while others are larger, like missing blocks of instructions. Yet both small and large bugs can shut down big systems. History records failures in air traffic control, hospital records, and government websites caused by such mistakes. Each time, people faced delays, stress, and fear until the error was corrected. The misplaced dot in the bank login page is only one example, but it is a sharp signal that technology is both powerful and fragile. The smallest detail carries weight, and carelessness carries a price.
The solution lies in discipline. Developers must write code with patience, treating every symbol with respect. Banks must insist on quality checks, demanding code reviews as part of their daily culture. Automated scanning tools exist today that can identify misplaced symbols and prevent errors. Regular updates and reviews make systems stronger. Training new programmers to value accuracy ensures the future remains secure. Just as a faithful servant proves trustworthy in little things, programmers who are faithful in small marks protect the greater system. In technology, faithfulness in details is not an option, it is the foundation.
This story also brings out the importance of humility in technology. The error was not a mighty attack from the outside. It was a human mistake from within. Accepting that mistakes will happen encourages the building of safety nets. Backup systems, error logs, and fallback pages are like guards that catch the fault before it spreads. When banks respect these measures, customers enjoy steady access, and confidence grows stronger. A working bank login page may appear simple on the surface, but behind it is a constant war against errors. Every line of code is part of that battle, and every symbol is a soldier.
The truth is clear. In life and in code, little things matter. Just as a spark can light up a forest, so can a misplaced dot stop an entire system. The day a dot broke a bank login page, thousands of customers were locked out. Yet the day it was corrected, peace was restored. This is the reality of technology, that strength lies in details, and confidence is built on discipline. Banks that guard their systems with careful eyes will continue to hold the trust of their people. Developers that respect every symbol will continue to create systems that stand firm. And customers who understand the hidden structure behind the screen will face errors with calm hearts, knowing that sometimes the smallest fix brings the greatest relief.
In conclusion, one misplaced dot was enough to break a bank login page. The dot changed the meaning of the code, blocked the server connection, and locked out thousands of customers. Yet, the solution was simply to place it back where it belonged. The story carries a strong signal for developers, banks, and customers alike. It proves that small details in digital banking security can have large effects in reality. When banks respect details, customers enjoy trust. When developers respect symbols, systems remain alive. And when everyone values accuracy, technology continues to serve with strength and stability.



 Edutech Portal3 weeks ago
Edutech Portal3 weeks agoInternet Sovereignty: Why Some Countries Want Their Own Separate Internet



 Digital Hustle3 weeks ago
Digital Hustle3 weeks agoHow One Misplaced Dot Broke a Bank Login Page


 Edutech Portal3 weeks ago
Edutech Portal3 weeks agoThe Untold Story Of The Nigerian Who Helped Build Global Internet Systems



 Edutech Portal3 weeks ago
Edutech Portal3 weeks agoNigerian Hackers: The Global Fraud Story and Its Fallout



 Edutech Portal3 weeks ago
Edutech Portal3 weeks agoForgotten Satellites Defy Silence, Beaming Signals for Decades



 Edutech Portal3 weeks ago
Edutech Portal3 weeks agoDo Not Allow Your Digital Store to Shut Down: The Exact Dates That Kill Websites



 Edutech Portal3 weeks ago
Edutech Portal3 weeks agoThe “Village People” Aren’t Blocking Your Sales; Your Bad SEO Is.



 Edutech Portal3 weeks ago
Edutech Portal3 weeks agoThe Business That Died because the Owner Refused to “Go Beyond.”