Uncategorized
The Leaking Bucket where State Revenue Often Vanishes
Discover how preventing revenue leakage in state government transforms public finance. Our analysis explores the digital bridge for fiscal expansion.

A government bank account without digital monitoring is a basket left under a heavy rain: much enters, but little resides for the morning. Public funds often evaporate before they reach the treasury. The silence in the halls of the Secretariat hides the sound of money escaping through manual receipt books and unmonitored cash points. Preventing revenue leakage in state government demands a system where human contact with cash resides in the past.
Manual records possess a strange habit of vanishing just before audit season begins. The paper trail in many ministries has more holes than a local sponge. Expecting a manual file to move during a public holiday is like expecting a dry tap to suddenly bring cold water. This reliance on physical paper creates a space where accountability fails.


The Silent Death of Public Funds
Revenue officers often carry paper receipts like sacred relics. These documents represent a vulnerability in the fiscal framework. A single misplaced book results in the loss of millions. The messenger leaning against the wall while waiting for a tip knows the secret: paper is slow, and slow systems allow for diversion.
Each kobo that fails to enter the treasury is a hospital bed that never arrives. The sound of rain hitting a rusted zinc roof so loud you fail to hear your own thoughts mirrors the chaos of uncoordinated tax collection. Without a unified system, different departments hunt the same taxpayers while the actual yield low.
Dr. Ngozi Okonjo-Iweala once observed a heavy truth regarding the finances of the nation:
“Leakages in the system represent the biggest challenge to fiscal stability and the ability of the state to serve the people.”
This observation highlights the requirement for a technological intervention. Preventing revenue leakage in state government requires the removal of the middleman who handles physical currency. When cash touches a hand before it touches a bank account, the risk of disappearance increases.
Building the digital bridge for Fiscal Expansion
We provide the digital bridge to connect the street where taxes are paid to the office where they are recorded. This connection ensures that the moment a citizen pays for a license, the treasury records the activity. No person can alter the record once it enters the database.
This strategy relies on automation to replace the heavy smell of old paper and damp archives in a basement registry. Modern administration moves at the speed of light, while manual processes move at the speed of a tired clerk. By adopting electronic portals, the state ensures that the total sum of collected funds reaches its destination.


Electronic validation replaces the physical presence of a signatory.
Digital systems create a permanent record of each transaction. If a payment occurs at a remote outpost, the headquarters sees it immediately. This visibility discourages the temptation to under-report collections. The state gains the ability to plan for expansion because the data is reliable.
The Reality of Direct Collection
Direct bank transfers and point-of-sale terminals change the nature of public service. A citizen who pays via a mobile app receives an instant receipt. This receipt is the shield of the citizen against harassment. It is also the guarantee of the state that the funds are secure.
Some operators prefer the old way because shadows provide cover for small thefts. However, the requirement for progress outweighs the comfort of the few. Preventing revenue leakage in state government is about the survival of the collective. When the bucket is whole, the water serves the entire community.
Professional advisors understand that technology is the only neutral referee in the game of finance. The digital bridge removes the bias of the collector. It ensures that the rules apply to a specific individual and the general public with equal force. This fairness encourages voluntary compliance among taxpayers.
Data as the New Currency of Governance
In the Space of the internet, information flows without the restrictions of physical distance. A Governor can view the revenue report on a phone while traveling between cities. This level of oversight was impossible in the era of leather-bound ledgers.
Expansion of the tax base happens more easily when people trust the system. If a person sees that their payment leads to a new road, they pay with less resistance. Transparency resides in the ability to track each naira from the point of entry to the point of expenditure.
As the late Chief Obafemi Awolowo once suggested regarding the management of public resources:
“The first duty of a government is to ensure that the resources of the people are managed with the highest level of integrity and care.”
Maintaining this integrity requires the abandonment of outdated methods. Preventing revenue leakage in state government is a moral obligation as much as a financial one. It protects the future of the state from the greed of the present.
The Path to Sustainable Yield
Realizing a high yield from internal revenue requires a focus on the user experience of the taxpayer. If the process of paying a tax is difficult, people avoid it. If the process is as simple as sending a text message, compliance rises.
Our role is to provide the framework that makes this simplicity possible. We eliminate the bottlenecks that slow down the movement of money. The result is a treasury that grows heavy with the contributions of a satisfied populace.
In conclusion, the leaking bucket of state finance can be mended. It requires the courage to replace the familiar paper with the efficient code. Preventing revenue leakage in state government ensures that the wealth of the land serves the needs of the children of the land. When the digital bridge is in place, the path to prosperity is wide and secure.
Uncategorized
Stop Being Busy, Start Being Productive – Focus on What Matters to Achieve Success
Uncategorized
How One Misplaced Dot Broke a Bank Login Page
A bank login page is more than just a simple screen on a website. It is the secure doorway that allows customers to reach their online accounts. Every time someone enters their username and password, the page serves as the bridge that connects the user with their money. When this page works perfectly, people enjoy smooth access. When it fails, confusion rises, and trust is shaken. What many do not know is that even a small detail, as tiny as a dot in computer code, can decide whether this door remains open or completely shut. There was a day when one misplaced dot broke a bank login page and locked out thousands of customers.
In daily life, a dot may look ordinary, simply ending a sentence. But in programming, a dot carries a higher weight. It links commands, guides actions, and connects pathways inside the code. Every dot has a position where it belongs. If that dot shifts, the whole meaning of the code changes. When the dot sits correctly, the instructions flow smoothly, and systems stay strong. But when it stands in the wrong place, the connection breaks, and the page collapses. This was exactly what happened in that bank login page error. A small misplaced dot blocked access and turned the page into a wall instead of a door.
When customers tried to log in, the page rejected every password, even when the details were correct. Error messages flashed, and people believed their accounts had been blocked. In truth, the accounts were safe, but the login script had lost its way. The misplaced dot confused the code, stopping it from speaking with the main server. What seemed like a massive cyber-attack was nothing more than a hidden syntax error. This error was small in size but great in effect. It proves once again that even a tiny seed can grow into a tree that affects many lives. In the same way, one symbol in the wrong place affected thousands of customers in one day.
The technical team of the bank was forced into action. They began a deep review of the code, reading line after line like scribes searching for a missing mark. At last, they found it. A single dot stood in the wrong place. It looked harmless, but it was the stone in the engine. Once the dot was moved back into its correct position, the entire bank login page came alive again. Customers could access their accounts, and the noise of fear began to fade. That correction, though small, restored confidence. It is a clear picture of how a little mistake can block the path, and a little correction can restore the light.
For developers and financial institutions, this case shines a light on three truths. First, it shows the necessity of code review. When more than one pair of eyes checks the script, hidden faults are easily discovered. The misplaced dot slipped through the first check, but a second review could have stopped the crisis before it began. Second, it reveals the value of a testing environment. This is a space where the system can be tested with fake accounts before it meets real customers. If the login page had gone through stronger testing, the dot would have been caught in silence. Third, it proves that every small detail matters in digital security. While banks build firewalls and strong encryption to fight hackers, they must also protect against simple human mistakes. A misplaced dot costs nothing to fix but can cost everything in customer trust.
For ordinary users, this story uncovers the hidden world behind every online banking login. People see only a clean page where they type details, but behind that page is a chain of codes stretching like an invisible ladder. If even one step on that ladder breaks, the climb becomes impossible. Customers should understand that many errors come from technical mistakes, not always from hackers. This knowledge reduces panic and allows patience while systems recover. But for the bank staff, the story is a strong call that the trust of the people rests on their attention to detail. When they watch carefully over every line of code, they protect not just data but also peace of mind.
The world of computing has seen many similar cases. Programmers call such mistakes bugs in software. Some are small, like this misplaced dot, while others are larger, like missing blocks of instructions. Yet both small and large bugs can shut down big systems. History records failures in air traffic control, hospital records, and government websites caused by such mistakes. Each time, people faced delays, stress, and fear until the error was corrected. The misplaced dot in the bank login page is only one example, but it is a sharp signal that technology is both powerful and fragile. The smallest detail carries weight, and carelessness carries a price.
The solution lies in discipline. Developers must write code with patience, treating every symbol with respect. Banks must insist on quality checks, demanding code reviews as part of their daily culture. Automated scanning tools exist today that can identify misplaced symbols and prevent errors. Regular updates and reviews make systems stronger. Training new programmers to value accuracy ensures the future remains secure. Just as a faithful servant proves trustworthy in little things, programmers who are faithful in small marks protect the greater system. In technology, faithfulness in details is not an option, it is the foundation.
This story also brings out the importance of humility in technology. The error was not a mighty attack from the outside. It was a human mistake from within. Accepting that mistakes will happen encourages the building of safety nets. Backup systems, error logs, and fallback pages are like guards that catch the fault before it spreads. When banks respect these measures, customers enjoy steady access, and confidence grows stronger. A working bank login page may appear simple on the surface, but behind it is a constant war against errors. Every line of code is part of that battle, and every symbol is a soldier.
The truth is clear. In life and in code, little things matter. Just as a spark can light up a forest, so can a misplaced dot stop an entire system. The day a dot broke a bank login page, thousands of customers were locked out. Yet the day it was corrected, peace was restored. This is the reality of technology, that strength lies in details, and confidence is built on discipline. Banks that guard their systems with careful eyes will continue to hold the trust of their people. Developers that respect every symbol will continue to create systems that stand firm. And customers who understand the hidden structure behind the screen will face errors with calm hearts, knowing that sometimes the smallest fix brings the greatest relief.
In conclusion, one misplaced dot was enough to break a bank login page. The dot changed the meaning of the code, blocked the server connection, and locked out thousands of customers. Yet, the solution was simply to place it back where it belonged. The story carries a strong signal for developers, banks, and customers alike. It proves that small details in digital banking security can have large effects in reality. When banks respect details, customers enjoy trust. When developers respect symbols, systems remain alive. And when everyone values accuracy, technology continues to serve with strength and stability.
Uncategorized
Nigerian Hackers: The Global Fraud Story and Its Fallout


The Story of Nigerian Hackers That Shook the World
The story of Nigerian hackers is one of the most unforgettable tales in the digital age. It is a record of how technology in the wrong hands can create waves across nations and shake mighty institutions. It is also a call for deeper wisdom, because when light enters darkness, nothing can remain hidden.
The global stage first began to hear about Nigerian hackers in the late 1990s and early 2000s. At that time, internet use was spreading quickly, but many people had little knowledge of online dangers. In that environment, groups of young Nigerians discovered that simple email messages could open doors to money. They crafted letters that promised sudden wealth, business opportunities, or love. These emails requested personal information or even small payments from strangers abroad. Many people believed and responded, and from there the scams grew. This practice later became famous as the “Nigerian Prince” scam. It looked simple, but it was powerful enough to shake global trust in email.
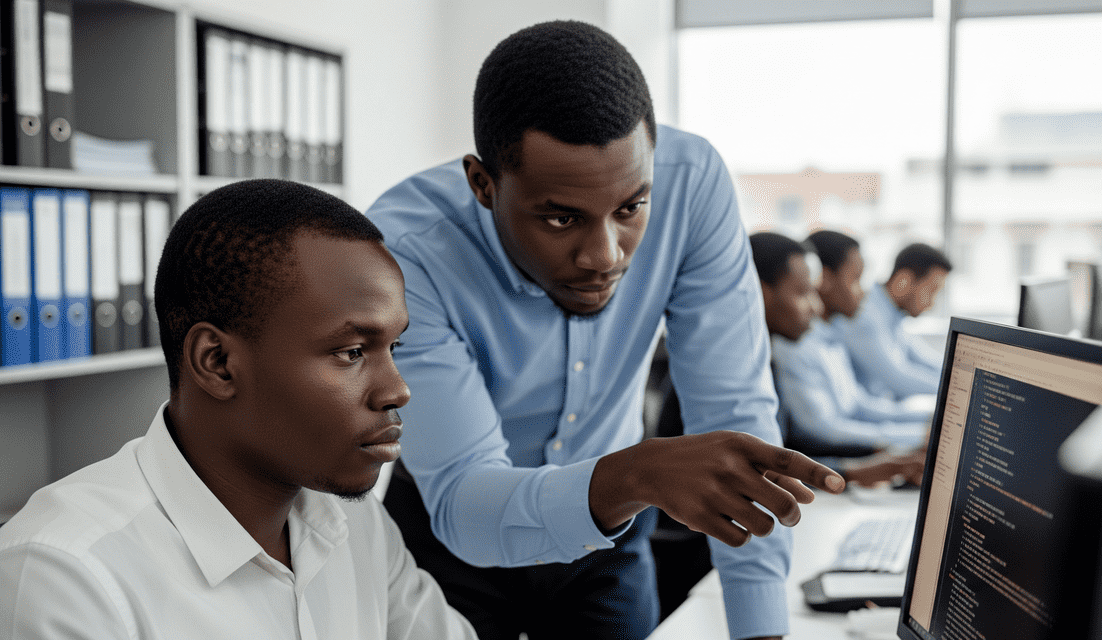
As years passed, cybercrime in Nigeria became more advanced. By the 2010s, it had grown far beyond email fraud. Hackers began to build fake websites, attack company databases, and use stolen credit card details to shop or move money. They built global networks that stretched across Europe, Asia, and America. Some even linked with international crime groups. The shock was that many of these hackers were young men, often with little formal training, yet they could break into systems that belonged to giant companies and governments. It showed the world a deeper truth, that even the small can confuse the strong.
One case that captured attention was the fall of Obinwanne Okeke (Invictus Obi). He was once celebrated as a bright young African entrepreneur and had even been listed by respected magazines as a model of success. Yet, in 2019, he was arrested in the United States and charged with fraud. Investigations revealed that his group had stolen millions of dollars from American companies through hacking and email compromise. His downfall became a headline because it showed how far Nigerian hackers had gone in infiltrating global businesses.
Another side of the story was the rise of the “Yahoo Boys.” This name came from the early days when Yahoo Mail was the platform of choice for scam messages. Over time, it became a cultural tag in Nigeria. Many of these young men were in their twenties or thirties. They became famous for driving expensive cars, wearing flashy designer outfits, and spending recklessly in public. Behind the glamour was a dark foundation of romance scams, stolen cards, and deceitful schemes. Their lifestyle made them visible, both to local communities and to international authorities. Some observers called it greed, while others saw it as a cry for survival in an economy with limited jobs.
By 2019, global authorities were already on high alert. The FBI, Interpol, and the EFCC in Nigeria began to work together. One of the biggest breakthroughs came with “Operation reWired,” where more than 200 suspects were arrested across different countries, including over 70 in Nigeria. It was one of the largest coordinated crackdowns on cybercrime. This operation proved that global cybercrime from Nigeria was real, massive, and too big to ignore.
The methods used by these hackers were equally shocking. One of the most dangerous was called Business Email Compromise (BEC). In this system, hackers gained access to the email account of a worker in a company. From there, they sent fake invoices or payment instructions to business partners. Because the email looked genuine, many companies sent millions of dollars to fraudulent accounts before they realized the deception. This type of attack affected businesses in the United States, United Kingdom, Asia, and other regions, making it one of the most damaging cybercrime strategies in the world.
The story also opened wider discussions about poverty, youth, and opportunity. Nigeria is a nation with over 200 million people, and most of them are young. Opportunities are limited, and graduates often face struggles. Some of these youths turned to cybercrime in Nigeria because they believed it was a faster route to wealth. Yet the gain was temporary, because many ended up in prison. This showed people the eternal truth that a man reaps what he sows.
But even while cybercrime created a negative picture, another side of Nigerian youth was rising. The same nation that produced Yahoo Boys also produced world-class fintech innovators, software developers, and digital start-ups. Nigerian technology hubs in Lagos, Abuja, and Port Harcourt began to show the creative power of the youth when guided in the right direction. While some chose destruction, others chose construction. This balance is necessary when telling the story of Nigerian hackers , because it is also a story of redemption and new possibilities.
The shock of these hackers forced banks, companies, and governments to strengthen their defenses. Two-factor authentication, stronger firewalls, and staff cybersecurity training became standard practice. Many organizations invested heavily in better monitoring systems. Losses caused by Nigerian hackers became the push that forced a global upgrade in digital safety. Out of the ashes of failure came lessons that built stronger foundations.
The Nigerian government also responded to the pressure. The EFCC increased raids, arrests, and prosecutions. In major cities like Lagos, Abuja, and Port Harcourt, reports of arrests filled the headlines often. These actions were important in restoring trust. Yet, as new hackers kept rising, the battle continued. Crime always grows quickly in places where opportunity is wide but discipline is weak, just like weeds sprout easily in an open field.
This wave of cybercrime also shaped how the world viewed Nigeria. On one side, the nation was celebrated for music, films, and creativity. On the other side, Nigerian hackers created suspicion that affected honest Nigerians abroad. Embassies and visa offices increased checks, and companies abroad sometimes hesitated to work with Nigerians. This was one of the silent burdens created by cybercrime.
To change the tide, education and awareness became necessary. Nigerian universities introduced cybersecurity courses. Non-profit groups started awareness campaigns to teach safe online behavior. Tech firms opened internships to redirect young talent into productive work. The goal was to transform youthful energy from destruction into construction.
Looking back, the story of Nigerian hackers is not only about fraud. It is also about how societies react to danger. It teaches the need for stronger values, fairer opportunities, and better global cooperation. It also proves that desire for fast wealth without discipline leads to collapse. A house built on sand may look strong, but it cannot endure storms.
Today, many hackers have been jailed, but cybercrime is still present in Nigeria and across the world. Yet the shock created by these events forced leaders, businesses, and communities to be more alert. The story will remain a reference point in the history of global cybersecurity.
Technology is a gift that opens doors to progress. But it must be guided with honesty and discipline. The future depends on raising strong walls, both in the digital space and in daily life. With wisdom, the same skills that once shook the world can build a brighter path for generations to come.



 Uncategorized1 day ago
Uncategorized1 day agoInternet Sovereignty: Why Some Countries Want Their Own Separate Internet



 Uncategorized1 day ago
Uncategorized1 day agoThe Smallest Change That Will Affect All Digital Operations



 Uncategorized1 day ago
Uncategorized1 day agoHow One Misplaced Dot Broke a Bank Login Page


 Uncategorized1 day ago
Uncategorized1 day agoThe Untold Story Of The Nigerian Who Helped Build Global Internet Systems



 Uncategorized1 day ago
Uncategorized1 day agoNigerian Hackers: The Global Fraud Story and Its Fallout



 Uncategorized1 day ago
Uncategorized1 day agoForgotten Satellites Defy Silence, Beaming Signals for Decades



 E-Commerce1 day ago
E-Commerce1 day agoDo Not Allow Your Digital Store to Shut Down:



 World on Fire1 day ago
World on Fire1 day agoNigeria Enter One Chance? Insecurity and Sachet Economy in 2026